Last Update 20 hours ago Total Questions : 30
The Fortinet NSE 5 - FortiEDR 5.0 Exam content is now fully updated, with all current exam questions added 20 hours ago. Deciding to include NSE5_EDR-5.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our NSE5_EDR-5.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these NSE5_EDR-5.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Fortinet NSE 5 - FortiEDR 5.0 Exam practice test comfortably within the allotted time.
An administrator needs to restrict access to the ADMINISTRATION tab in the central manager for a specific account.
What role should the administrator assign to this account?
Refer to the exhibit.
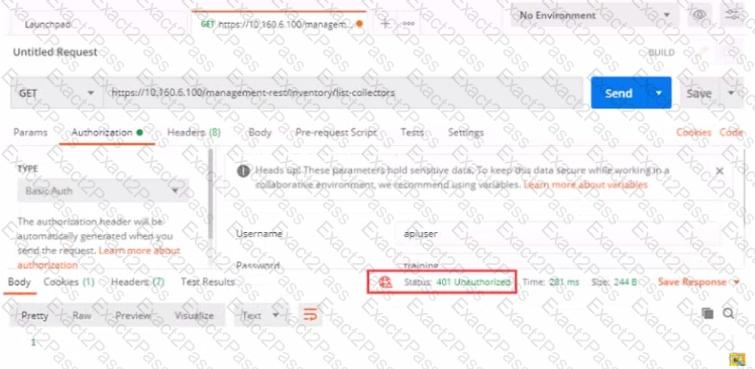
Based on the postman output shown in the exhibit why is the user getting an unauthorized error?
Which security policy has all of its rules disabled by default?
The FortiEDR axe classified an event as inconclusive, out a few seconds later FCS revised the classification to malicious. What playbook actions ate applied to the event?
An administrator finds a third party free software on a user's computer mat does not appear in me application list in the communication control console
Which two statements are true about this situation? (Choose two)
What is the benefit of using file hash along with the file name in a threat hunting repository search?

