Last Update 17 hours ago Total Questions : 390
The HCIA-Datacom V1.0 Exam content is now fully updated, with all current exam questions added 17 hours ago. Deciding to include H12-811_V1.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-811_V1.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-811_V1.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIA-Datacom V1.0 Exam practice test comfortably within the allotted time.
What is the total length of the VLAN frame defined by IEEE 802.1Q?
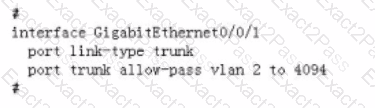
According to the command output shown in the figure, which of the following statements are true?
Which of the following port states is not included in Rapid Spanning Tree Protocol (RSTP)?
Which extension headers are supported by IPv6 packets?
To provide the information about the IP addresses that a user packet traverses along the path to the destination, which of the following does Tracert record in each expired ICMP TTL packet?
Which of the following commands is used to display the CPU usage of a router?
Which of the following network types does OSPF support?

