Last Update 8 hours ago Total Questions : 367
The HCIP-Security (Fast track) V1.0 content is now fully updated, with all current exam questions added 8 hours ago. Deciding to include H12-724 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-724 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-724 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIP-Security (Fast track) V1.0 practice test comfortably within the allotted time.
According to the different user name format and content used by the access device to verify user identity, the user name format used for MAC authentication can be changed.
There are three types. Which of the following formats is not included?
In the security protection system of the cloud era, reforms need to be carried out in the three stages before, during and after the event, and a closed-loop continuous improvement should be formed.
And development. Which of the following key points should be done in "things"? (multiple choice)
Which of the following technology, administrators can according to business requirements, to scale to achieve load sharing of business flow?
Regarding asset management, which of the following descriptions is wrong?
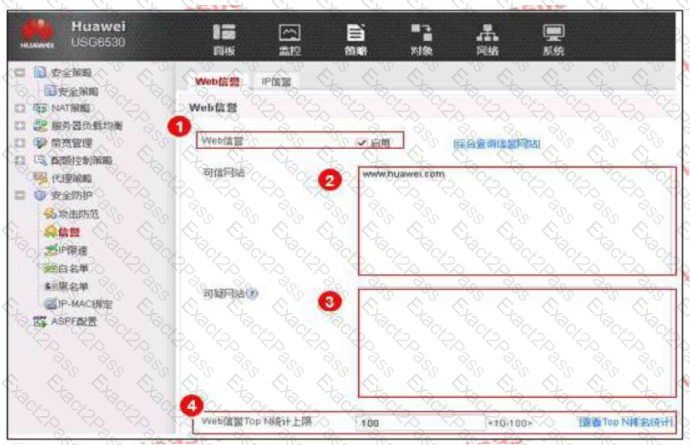
An enterprise administrator configures the Web reputation system as shown in the figure. Regarding the configuration, which of the following statements is correct?
Windows in environment,Agile Controller-Campus After the installation is successful, how to manually start the management center(MC)? (Multiple choice)
The core technology of content security lies in anomaly detection, and the concept of defense lies in continuous monitoring and analysis.

