Last Update 18 hours ago Total Questions : 196
The HCIP-Security-CSSN V3.0 content is now fully updated, with all current exam questions added 18 hours ago. Deciding to include H12-722_V3.0 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our H12-722_V3.0 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these H12-722_V3.0 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any HCIP-Security-CSSN V3.0 practice test comfortably within the allotted time.
Which of the following options is not a cyber security threat caused by weak personal security awareness?
Which of the following options does not belong to the basic DDoS attack prevention configuration process?
The following figure is a schematic diagram of the detection file of the firewall and the sandbox system linkage.
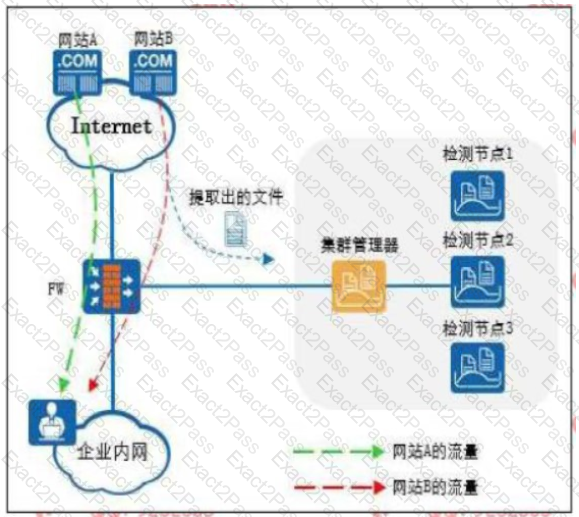
The Web reputation function is enabled on the firewall, and website A is set as a trusted website and website B is set as a suspicious website.
Which of the following statements is correct
Regarding the processing flow of file filtering, which of the following statements is wrong?
SACG query right-manager information as follows, which options are correct? (Select 2 answers)

Which of the following options will not pose a security threat to the network?
Which of the following options is not a feature of Trojan horses?

