Last Update 19 hours ago Total Questions : 89
The FCP - FortiGate 7.4 Administrator content is now fully updated, with all current exam questions added 19 hours ago. Deciding to include FCP_FGT_AD-7.4 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our FCP_FGT_AD-7.4 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these FCP_FGT_AD-7.4 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any FCP - FortiGate 7.4 Administrator practice test comfortably within the allotted time.
Refer to the exhibit.
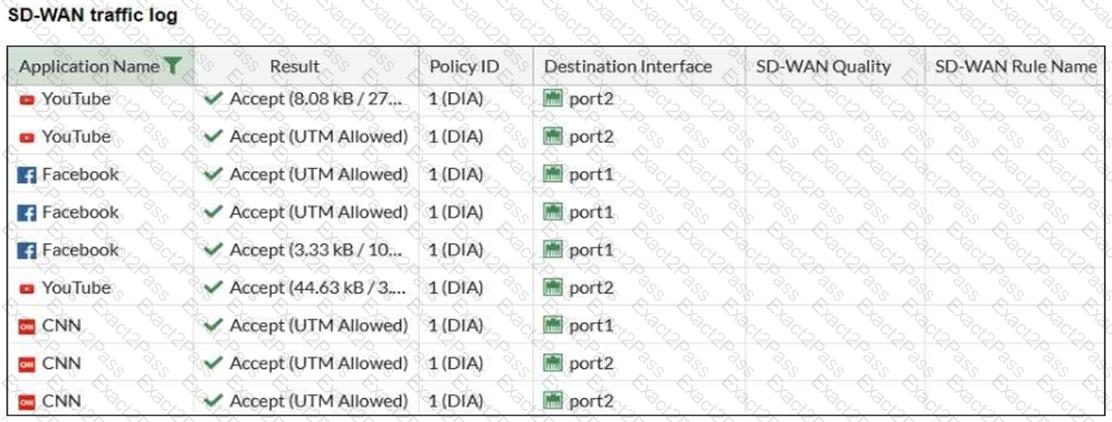
The administrator configured SD-WAN rules and set the FortiGate traffic log page to display SD-WAN-specific columns: SD-WAN Quality and SD-WAN Rule Name.
FortiGate allows the traffic according to policy ID 1. This is the policy that allows SD-WAN traffic.
Despite these settings the traffic logs do not show the name of the SD-WAN rule used to steer those traffic flows.
What can be the reason?
Refer to the exhibits, which show the system performance output and the default configuration of high memory usage thresholds in a FortiGate.
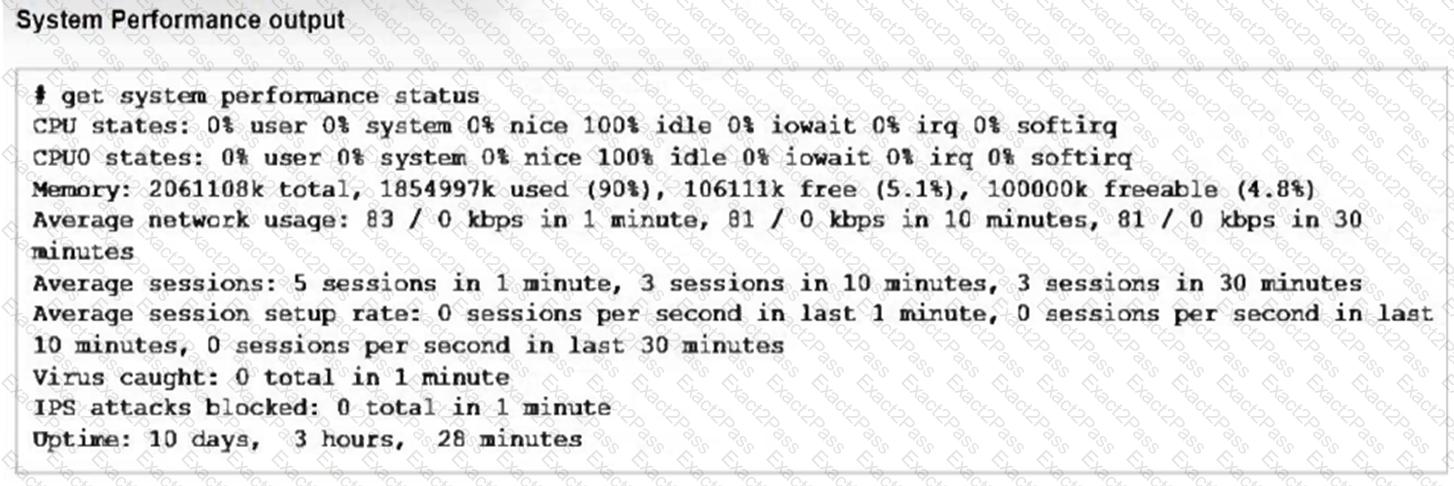
Based on the system performance output, what can be the two possible outcomes? (Choose two.)
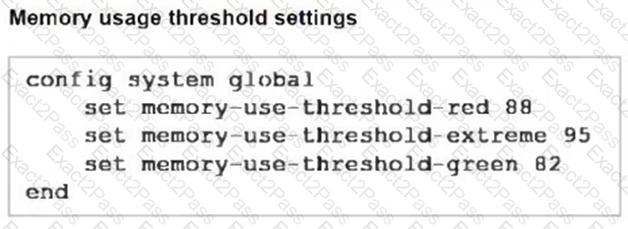
Refer to the exhibit, which shows a partial configuration from the remote authentication server.
Why does the FortiGate administrator need this configuration?
Which engine handles application control traffic on the next-generation firewall (NGFW) FortiGate?
What are two features of FortiGate FSSO agentless polling mode? (Choose two.)
Which three CLI commands, can you use to troubleshoot Layer 3 issues if the issue is in neither the physical layer nor the link layer? (Choose three.)
Refer to the exhibit which contains a RADIUS server configuration.
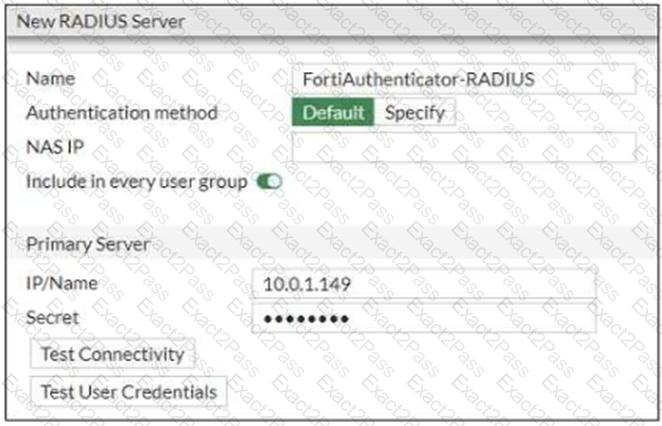
An administrator added a configuration for a new RADIUS server. While configuring, the administrator selected the Include in every user group option.
What is the impact of using the Include in every user group option in a RADIUS configuration?

