Last Update 19 hours ago Total Questions : 878
The Ethical Hacking and Countermeasures V8 content is now fully updated, with all current exam questions added 19 hours ago. Deciding to include EC0-350 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our EC0-350 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these EC0-350 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Ethical Hacking and Countermeasures V8 practice test comfortably within the allotted time.
William has received a Chess game from someone in his computer programming class through email. William does not really know the person who sent the game very well, but decides to install the game anyway because he really likes Chess.

After William installs the game, he plays it for a couple of hours. The next day, William plays the Chess game again and notices that his machine has begun to slow down. He brings up his Task Manager and sees the following programs running:
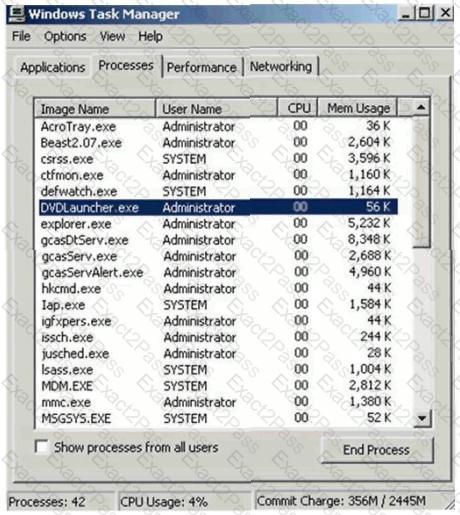
What has William just installed?
Exhibit
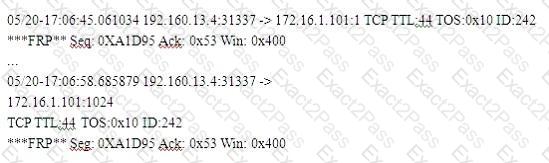
(Note: the student is being tested on concepts learnt during passive OS fingerprinting, basic TCP/IP connection concepts and the ability to read packet signatures from a sniff dump.)
Snort has been used to capture packets on the network. On studying the packets, the penetration tester finds it to be abnormal. If you were the penetration tester, why would you find this abnormal?
What is odd about this attack? Choose the best answer.
Which of the following is a common Service Oriented Architecture (SOA) vulnerability?
What techniques would you use to evade IDS during a Port Scan? (Select 4 answers)
Which type of scan measures a person ' s external features through a digital video camera?
John is discussing security with Jane. Jane had mentioned to John earlier that she suspects an LKM has been installed on her server. She believes this is the reason that the server has been acting erratically lately. LKM stands for Loadable Kernel Module.
What does this mean in the context of Linux Security?
Steven the hacker realizes that the network administrator of XYZ is using syskey to protect organization resources in the Windows 2000 Server. Syskey independently encrypts the hashes so that physical access to the server, tapes, or ERDs is only first step to cracking the passwords. Steven must break through the encryption used by syskey before he can attempt to brute force dictionary attacks on the hashes. Steven runs a program called “SysCracker” targeting the Windows 2000 Server machine in attempting to crack the hash used by Syskey. He needs to configure the encryption level before he can launch attach.
How many bits does Syskey use for encryption?
What are the two basic types of attacks? (Choose two.
NSLookup is a good tool to use to gain additional information about a target network. What does the following command accomplish?
nslookup
> server < ipaddress >
> set type =any
> ls -d < target.com >
What statement is true regarding LM hashes?
The fundamental difference between symmetric and asymmetric key cryptographic systems is that symmetric key cryptography uses which of the following?
How does an operating system protect the passwords used for account logins?
You are the CIO for Avantes Finance International, a global finance company based in Geneva. You are responsible for network functions and logical security throughout the entire corporation. Your company has over 250 servers running Windows Server, 5000 workstations running Windows Vista, and 200 mobile users working from laptops on Windows 7.
Last week, 10 of your company ' s laptops were stolen from salesmen while at a conference in Amsterdam. These laptops contained proprietary company information. While doing damage assessment on the possible public relations nightmare this may become, a news story leaks about the stolen laptops and also that sensitive information from those computers was posted to a blog online.
What built-in Windows feature could you have implemented to protect the sensitive information on these laptops?
Lee is using Wireshark to log traffic on his network. He notices a number of packets being directed to an internal IP from an outside IP where the packets are ICMP and their size is around 65, 536 bytes. What is Lee seeing here?
Which of the following systems would not respond correctly to an nmap XMAS scan?
While reviewing the result of scanning run against a target network you come across the following:
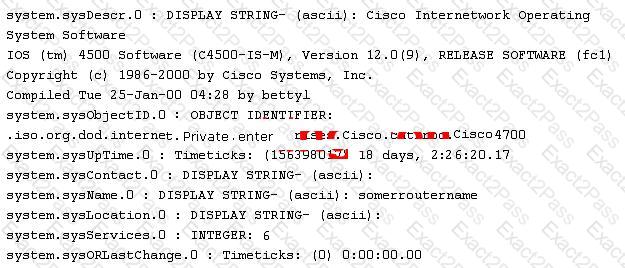
Which among the following can be used to get this output?
Which type of antenna is used in wireless communication?

