Last Update 13 hours ago Total Questions : 736
The Certified Professional Ethical Hacker (CPEH) content is now fully updated, with all current exam questions added 13 hours ago. Deciding to include CPEH-001 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our CPEH-001 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these CPEH-001 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any Certified Professional Ethical Hacker (CPEH) practice test comfortably within the allotted time.
How can telnet be used to fingerprint a web server?
Eve is spending her day scanning the library computers. She notices that Alice is using a computer whose port 445 is active and listening. Eve uses the ENUM tool to enumerate Alice machine. From the command prompt, she types the following command.
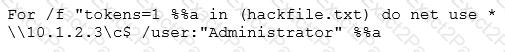
What is Eve trying to do?
Which of the following techniques does a vulnerability scanner use in order to detect a vulnerability on a target service?
A security engineer is attempting to map a company’s internal network. The engineer enters in the following NMAP command:
NMAP –n –sS –P0 –p 80 ***.***.**.**
What type of scan is this?
The company ABC recently discovered that their new product was released by the opposition before their premiere. They contract an investigator who discovered that the maid threw away papers with confidential information about the new product and the opposition found it in the garbage. What is the name of the technique used by the opposition?
In the context of password security, a simple dictionary attack involves loading a dictionary file (a text file full of dictionary words) into a cracking application such as L0phtCrack or John the Ripper, and running it against user accounts located by the application. The larger the word and word fragment selection, the more effective the dictionary attack is. The brute force method is the most inclusive, although slow. It usually tries every possible letter and number combination in its automated exploration. If you would use both brute force and dictionary methods combined together to have variation of words, what would you call such an attack?
Fingerprinting VPN firewalls is possible with which of the following tools?
What is one of the advantages of using both symmetric and asymmetric cryptography in SSL/TLS?
Bob finished a C programming course and created a small C application to monitor the network traffic and produce alerts when any origin sends “many” IP packets, based on the average number of packets sent by all origins and using some thresholds.
In concept, the solution developed by Bob is actually:
Nedved is an IT Security Manager of a bank in his country. One day. he found out that there is a security breach to his company ' s email server based on analysis of a suspicious connection from the email server to an unknown IP Address.
What is the first thing that Nedved needs to do before contacting the incident response team?
The network team has well-established procedures to follow for creating new rules on the firewall. This includes having approval from a manager prior to implementing any new rules. While reviewing the firewall configuration, you notice a recently implemented rule but cannot locate manager approval for it. What would be a good step to have in the procedures for a situation like this?
Analyst is investigating proxy logs and found out that one of the internal user visited website storing suspicious Java scripts. After opening one of them, he noticed that it is very hard to understand the code and that all codes differ from the typical Java script. What is the name of this technique to hide the code and extend analysis time?

