Last Update 19 hours ago Total Questions : 201
The EC-Council Certified Security Analyst (ECSA) V10 content is now fully updated, with all current exam questions added 19 hours ago. Deciding to include 412-79v10 practice exam questions in your study plan goes far beyond basic test preparation.
You'll find that our 412-79v10 exam questions frequently feature detailed scenarios and practical problem-solving exercises that directly mirror industry challenges. Engaging with these 412-79v10 sample sets allows you to effectively manage your time and pace yourself, giving you the ability to finish any EC-Council Certified Security Analyst (ECSA) V10 practice test comfortably within the allotted time.
A penetration test will show you the vulnerabilities in the target system and the risks associated with it. An educated valuation of the risk will be performed so that the vulnerabilities can be reported as High/Medium/Low risk issues.

What are the two types of ‘white-box’ penetration testing?
Identify the type of testing that is carried out without giving any information to the employees or administrative head of the organization.
John, a penetration tester from a pen test firm, was asked to collect information about the host file in a Windows system directory. Which of the following is the location of the host file in Window system directory?
In which of the following firewalls are the incoming or outgoing packets blocked from accessing services for which there is no proxy?
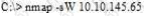
What operating system would respond to the following command?
How many possible sequence number combinations are there in TCP/IP protocol?
Jim performed a vulnerability analysis on his network and found no potential problems. He runs another utility that executes exploits against his system to verify the results of the vulnerability test. The second utility executes five known exploits against his network in which the vulnerability analysis said were not exploitable.
What kind of results did Jim receive from his vulnerability analysis?
Internet Control Message Protocol (ICMP) messages occur in many situations, such as whenever a datagram cannot reach the destination or the gateway does not have the buffering capacity to forward a datagram.
Each ICMP message contains three fields: type, code, and checksum. Different types of Internet Control Message Protocols (ICMPs) are identified by a TYPE field.
If the destination is not reachable, which one of the following are generated?
The first phase of the penetration testing plan is to develop the scope of the project in consultation with the client. Pen testing test components depend on the client’s operating environment, threat perception, security and compliance requirements, ROE, and budget.
Various components need to be considered for testing while developing the scope of the project.

Which of the following is NOT a pen testing component to be tested?
In the process of hacking a web application, attackers manipulate the HTTP requests to subvert the application authorization schemes by modifying input fields that relate to the user ID, username, access group, cost, file names, file identifiers, etc.
They first access the web application using a low privileged account and then escalate privileges to access protected resources. What attack has been carried out?

